Azure Virtual Desktop Setup Guide: Everything You Need to Know
Setting up Azure Virtual Desktop (AVD) involves five core stages: provisioning your Azure subscription with the right licensing, configuring your Active Directory environment, creating a host pool, deploying session host virtual machines, and assigning users to application groups. When done correctly, the result is a fully managed, scalable cloud desktop that your team can access securely from anywhere in the world.
This guide walks you through every step of the Azure Virtual Desktop setup process — from prerequisites to post-deployment validation — with expert tips on cost optimization, security hardening, and common troubleshooting. Whether you’re an IT admin setting up AVD for the first time or evaluating whether managed AVD services are a better fit for your business, this guide gives you everything you need to make an informed decision.
What You’ll Learn:
- What Azure Virtual Desktop is and how it works in 2026
- Exact prerequisites and licensing requirements before you start
- Step-by-step host pool, workspace, and session host configuration
- FSLogix profile container setup for persistent user profiles
- Security, compliance, cost optimization, and troubleshooting guidance
- How Apps4Rent simplifies and manages the entire AVD environment for you
What is Azure Virtual Desktop?
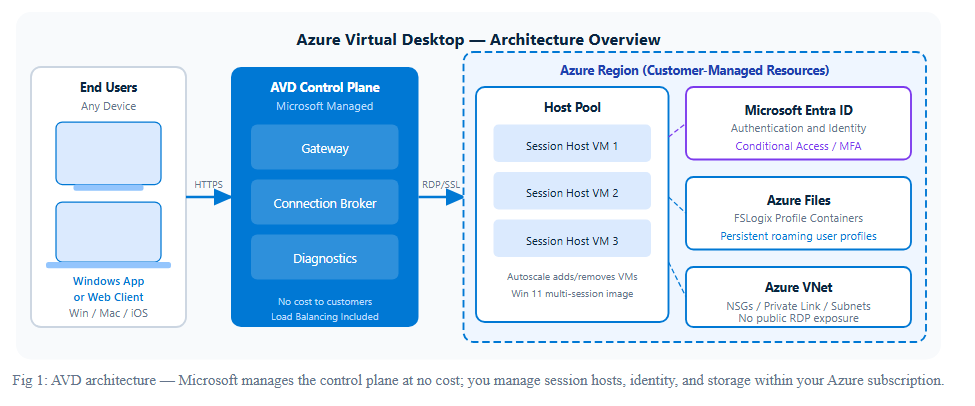
Azure Virtual Desktop (AVD) — formerly known as Windows Virtual Desktop (WVD) — is Microsoft’s cloud-based Desktop-as-a-Service (DaaS) platform hosted on Azure. It enables organizations to deliver Windows desktops and applications to any user, on any device, from anywhere in the world, without requiring physical hardware for each employee.
Unlike traditional VDI (Virtual Desktop Infrastructure), which requires on-premises servers and complex management, AVD runs entirely in the Microsoft Azure cloud. Microsoft manages the underlying infrastructure — including the control plane, load balancing, and gateway services — while your IT team (or a managed service provider like Apps4Rent) manages the session hosts, applications, and user policies.
At its core, Azure Virtual Desktop works through four primary components:
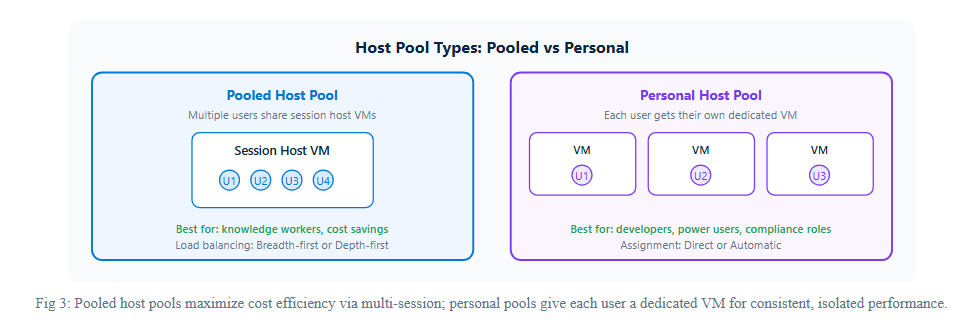
- Host Pools: A collection of Azure virtual machines (session hosts) that deliver desktops and apps to users. Host pools can be pooled (shared among multiple users) or personal (dedicated to a single user).
- Session Hosts: The Windows virtual machines within a host pool where user sessions actually run. These are Azure VMs running Windows 10/11 Enterprise multi-session or Windows Server.
- Workspaces: A logical grouping of application groups that users see in their AVD client. A workspace organizes the desktops and remote apps made available to users.
- Application Groups: Collections of applications or desktops published to users from a host pool. There are two types: desktop application groups (full desktops) and RemoteApp application groups (individual apps).
One of AVD’s most powerful differentiators is support for Windows 10 and Windows 11 Enterprise multi-session — an Azure-exclusive feature that allows multiple concurrent users to share a single VM session, dramatically reducing infrastructure costs compared to traditional VDI deployments.
AVD also integrates natively with Microsoft Entra ID (formerly Azure AD), Microsoft Intune, Microsoft Defender, and the full Microsoft 365 ecosystem, making it the logical cloud desktop choice for organizations already invested in Microsoft technology.
Why Choose Azure Virtual Desktop in 2026?
The remote work landscape has evolved significantly, and in 2026, Azure Virtual Desktop has solidified its position as the enterprise standard for cloud desktops. Here is why thousands of businesses are choosing AVD over legacy VDI and competing DaaS solutions:
- Unmatched Microsoft Integration: AVD is the only DaaS solution with native support for Windows 10/11 Enterprise multi-session, Microsoft 365 Apps optimization, Teams media offloading, and OneDrive Known Folder Move — capabilities unavailable on competing platforms.
- Cost Efficiency Through Multi-Session: By running multiple user sessions on a single VM, organizations typically reduce compute costs by 30–70% compared to single-session VDI deployments.
- Global Scale on Azure’s Infrastructure: AVD is available in over 60 Azure regions worldwide, enabling low-latency desktop delivery to users in virtually any geography.
- Zero Control Plane Cost: Microsoft operates and charges nothing for the AVD control plane (gateway, broker, diagnostics) — you pay only for the Azure resources you consume, such as VMs, storage, and networking.
- Built-In Security and Compliance: AVD integrates with Microsoft Defender for Cloud, Azure Security Center, Conditional Access, and Microsoft Purview to meet HIPAA, SOC 2, ISO 27001, and other compliance frameworks out of the box.
- Flexible Licensing: Users with eligible Microsoft 365 or Windows licenses can access AVD at no additional per-user access fee, dramatically reducing total cost of ownership.
For organizations comparing AVD with Windows 365, see our detailed comparison: Windows 365 Cloud PC vs Azure Virtual Desktop — the right choice depends on your technical capacity, customization needs, and budget model.
Prerequisites for Azure Virtual Desktop Setup
Before you begin the Azure Virtual Desktop setup process, you need to verify that your environment meets a set of foundational requirements. Skipping this step is the single most common reason AVD deployments fail or underperform. Here is what you need to have in place.
Azure Subscription & Licensing
An active Azure subscription is the baseline requirement. Within that subscription, you need sufficient permissions — specifically the Owner or Contributor role at the resource group level, plus the Desktop Virtualization Contributor role — to create and manage AVD resources.
For licensing, Azure Virtual Desktop access rights are included with the following Microsoft 365 and Windows licenses (no additional per-user fee required):
- Microsoft 365 E3, E5, F3
- Microsoft 365 Business Premium
- Windows 10/11 Enterprise E3 or E5
- Windows 10/11 VDA (Virtual Desktop Access)
- Remote Desktop Services (RDS) Client Access License (CAL) with Software Assurance (for Windows Server session hosts)
| License | AVD Access Included | Multi-Session Support | Best For |
| Microsoft 365 E3 / E5 | Yes — no extra fee | Yes | Enterprise organizations |
| Microsoft 365 Business Premium | Yes — no extra fee | Yes | SMBs up to 300 users |
| Microsoft 365 F3 | Yes — no extra fee | Yes | Frontline / shift workers |
| Windows 10/11 Enterprise E3 | Yes — no extra fee | Yes | Windows-only deployments |
| Windows 10/11 VDA | Yes — no extra fee | Yes | BYOD / unmanaged devices |
| RDS CAL + Software Assurance | Yes — Windows Server only | Yes (Server OS) | Legacy server-based sessions |
You will also be billed for the Azure compute (VMs), storage, and networking resources consumed by your AVD environment. These costs vary based on VM size, region, and usage patterns — which we cover in detail in the Cost Optimization section below.
Active Directory / Azure AD Setup
Azure Virtual Desktop requires an identity provider for authenticating users and joining session host VMs to a domain. In 2026, AVD supports three domain join options:
- Microsoft Entra ID Join (formerly Azure AD Join): The modern, cloud-native option. Session hosts are joined directly to Entra ID without requiring any on-premises Active Directory or domain controllers. This is the recommended approach for cloud-first organizations.
- Active Directory Domain Services (AD DS) Join: Traditional domain join. Requires at least one AD DS domain controller accessible from the AVD virtual network — either on-premises (connected via VPN or ExpressRoute) or hosted as an Azure VM. AD DS must sync to Microsoft Entra ID via Microsoft Entra Connect.
- Microsoft Entra Domain Services (AADS) Join: A managed AD DS service in Azure that eliminates the need to manage domain controllers. Ideal for organizations that need AD DS features (like Group Policy) without maintaining DC infrastructure.
Regardless of the join method, user accounts must exist in Microsoft Entra ID (either natively or synced from AD DS) and must be assigned valid AVD licenses before they can connect to sessions.
Network & Virtual Machine Requirements
Your Azure networking setup directly impacts AVD performance, security, and compliance. Here is what you need to configure before deployment:
- Azure Virtual Network (VNet): All session host VMs must reside within an Azure VNet. The VNet must have a subnet dedicated to AVD session hosts with sufficient IP address space for current and future VMs.
- DNS Configuration: For AD DS or AADS joins, the VNet’s DNS servers must be set to resolve the domain correctly — typically pointing to your domain controller IPs rather than Azure’s default DNS.
- Network Security Groups (NSGs): Configure NSGs to allow AVD traffic. Required outbound connectivity includes Azure Virtual Desktop service endpoints, Azure Active Directory endpoints, and Windows Update services. Inbound RDP (port 3389) from the internet should be blocked — users connect through the AVD Gateway, not directly.
- VM Size and Configuration: Microsoft recommends a minimum of 4 vCPUs and 16 GB RAM per session host for multi-session deployments. For knowledge workers, the D-series VMs (e.g., Standard_D4s_v5) deliver a strong performance-to-cost ratio. GPU-enabled VMs (NV-series) are required for graphics-intensive workloads such as CAD or video editing.
- Azure Files or Azure NetApp Files (for FSLogix): You need a file share service to store FSLogix user profile containers. Azure Files (SMB) is the standard choice for most deployments; Azure NetApp Files offers higher performance for large-scale or latency-sensitive environments.
Use the table below to select the right Azure VM size for your session hosts based on user workload profile:
| Workload Type | Recommended VM SKU | vCPU / RAM | Concurrent Users per VM | Typical Use Case |
| Light | Standard_D2s_v5 | 2 vCPU / 8 GB | 4–6 users | Email, web browsing, basic Office tasks |
| Medium | Standard_D4s_v5 | 4 vCPU / 16 GB | 6–10 users | Microsoft 365 Apps, line-of-business apps, Teams |
| Heavy | Standard_D8s_v5 | 8 vCPU / 32 GB | 8–12 users | Data processing, large Excel files, ERP systems |
| Power User | Standard_D16s_v5 | 16 vCPU / 64 GB | 1–4 users (personal) | Software development, compilation, heavy multi-tasking |
| GPU / Graphics | Standard_NV6ads_A10_v5 | 6 vCPU / 55 GB + GPU | 1–2 users (personal) | CAD, 3D rendering, video editing, GIS |
Step-by-Step Azure Virtual Desktop Setup
With prerequisites in place, you are ready to deploy Azure Virtual Desktop. The following steps use the Azure portal, which provides a guided wizard experience. Advanced deployments can use Azure CLI, PowerShell, Bicep templates, or Terraform for repeatable, infrastructure-as-code deployments.
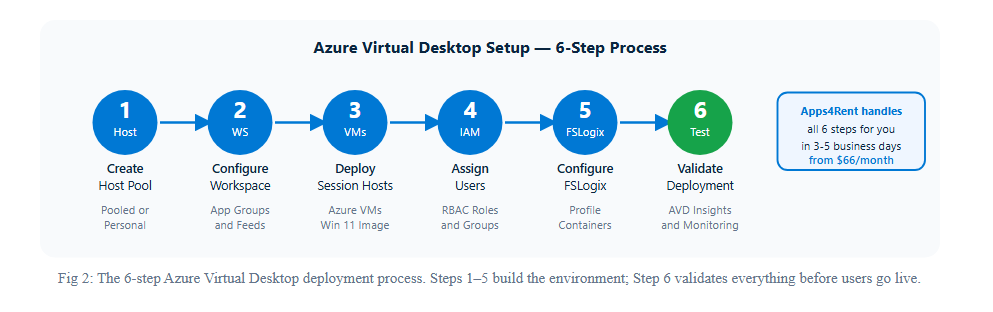
Step 1: Create a Host Pool
The host pool is the foundational container for your Azure Virtual Desktop environment. Every session host VM belongs to a host pool, and the host pool defines the load-balancing algorithm, session limits, and RDP properties applied to all sessions within it.
How to create a host pool in the Azure portal:
- Navigate to the Azure portal and search for Azure Virtual Desktop. Select Host pools from the left menu, then click + Create.
- On the Basics tab, enter a Host pool name, select your Subscription, Resource group, and Location (choose the Azure region geographically closest to your users for lowest latency).
- Choose Host pool type: Pooled (shared among multiple users — recommended for knowledge workers to maximize cost efficiency) or Personal (dedicated to individual users — ideal for developers, power users, or compliance-sensitive roles).
- For pooled host pools, set the Load balancing algorithm: Breadth-first (distributes users across all available VMs — best for multi-session efficiency) or Depth-first (fills one VM completely before moving to the next — better for autoscale cost savings).
- Set the Max session limit — the maximum number of concurrent user sessions per session host VM. Microsoft’s sizing guidelines recommend 4–6 users per vCPU for knowledge workers as a starting baseline.
- Under Agent update, configure your preferred agent update schedule to control when AVD agent updates are applied to your session hosts — important for avoiding unplanned disruptions in production environments.
Click Next: Virtual Machines to configure session hosts, or click Review + Create if you intend to add session hosts separately after pool creation.
Step 2: Configure Workspace
A workspace is the logical container that organizes and presents application groups to your end users. When users open the AVD client (Windows App or the Remote Desktop client), they see workspaces and the desktops or apps published within them.
Creating or linking a workspace during host pool creation:
- On the Workspace tab of the host pool creation wizard, choose whether to Register a new workspace or Register an existing workspace.
- If creating a new workspace, enter a Workspace name that is descriptive and recognizable to end users — this is the name they will see in their AVD client.
- The wizard automatically creates a default Desktop application group associated with the host pool and registers it to the workspace. This application group publishes the full Windows desktop to assigned users.
- To publish individual applications instead of (or in addition to) the full desktop, you will create a RemoteApp application group after initial deployment, add the specific applications, and register it to the same workspace.
Best practice: Use separate workspaces for different user groups (e.g., Finance workspace, Development workspace, General Staff workspace) to improve organization and simplify application group management as your environment grows.
Step 3: Deploy Session Hosts
Session hosts are the Azure VMs where user desktop sessions run. This is the most resource-intensive step of the AVD setup and directly determines the performance, scalability, and cost of your deployment.
Configuring session hosts in the host pool wizard:
- On the Virtual Machines tab, toggle Add Azure virtual machines to Yes.
- Enter a Name prefix for your VMs (e.g., avd-prod-) — the wizard appends a sequential number to each VM (avd-prod-0, avd-prod-1, etc.).
- Select the Virtual machine location — this should match your host pool location and be in the same region as your VNet for lowest latency.
- Choose your Image: For most deployments, select Windows 11 Enterprise multi-session + Microsoft 365 Apps from the Azure Marketplace gallery. This image includes the optimized Office 365 stack and is pre-configured for AVD multi-session usage. Use Windows 10 multi-session images only if you have specific compatibility requirements.
- Select the Virtual machine size based on your user workload profile. Standard_D4s_v5 (4 vCPUs, 16 GB RAM) is a solid starting point for 6–8 concurrent knowledge workers per VM.
- Specify the Number of VMs to deploy. For a pilot deployment, start with 2 VMs to ensure high availability. Scale horizontally using autoscale policies post-deployment.
- Under OS disk type, select Premium SSD for production environments. Standard SSDs are acceptable for dev/test. HDDs are not recommended for AVD session hosts due to their impact on logon times and application launch speeds.
- Configure Network and security: Select the VNet and subnet prepared in your prerequisites. Ensure Public inbound ports is set to None — users access session hosts exclusively through the AVD secure gateway, never directly via RDP.
- Under Domain to join, choose your domain join method (Entra ID, AD DS, or AADS) and provide the credentials required to join the domain.
After review, the wizard deploys the VMs, installs the AVD agent and boot loader, joins them to the domain, and registers them with the host pool — all automatically.
Step 4: Assign Users & Permissions
With the host pool, workspace, and session hosts deployed, the next step is granting users access to their desktops and applications. In AVD, access is controlled through role assignments on application groups — not on the VMs or the host pool directly.
Assigning users to the desktop application group:
- In the Azure portal, navigate to Azure Virtual Desktop > Application groups and select the desktop application group created with your host pool.
- Go to Access control (IAM) and click + Add > Add role assignment.
- Select the Desktop Virtualization User role and assign it to the users or security groups that should have access to this desktop. Using Entra ID security groups rather than individual users makes ongoing management significantly easier — add or remove users from the group rather than modifying role assignments each time.
- Verify that assigned users have valid AVD-eligible licenses (Microsoft 365 E3/E5, Microsoft 365 Business Premium, Windows Enterprise E3/E5, or Windows VDA) applied to their Entra ID accounts.
- For RemoteApp application groups, publish individual applications through the Applications menu within the application group, then assign users via IAM in the same manner.
Important: Users must also be granted VM login rights on the session host VMs. For Entra ID-joined VMs, assign the Virtual Machine User Login role (for standard users) or Virtual Machine Administrator Login role (for admins) at the resource group or VM level.
Step 5: Configure FSLogix Profile Containers
FSLogix profile containers are one of the most critical — and most frequently skipped — components of a well-functioning AVD deployment. Without FSLogix, users lose their profile data (desktop settings, application configurations, browser bookmarks, Outlook cache) every time they log off in a pooled host pool, because they may land on a different VM at next login.
FSLogix stores the entire user profile as a VHD/VHDX file on a central file share (Azure Files or Azure NetApp Files), which is dynamically mounted to whatever session host the user connects to — making the profile experience identical regardless of which VM serves the session.
Setting up FSLogix profile containers:
- Create an Azure Files share: In your Azure storage account, create a file share dedicated to FSLogix profiles. Enable Active Directory authentication on the storage account — either AD DS-based or Entra ID-based, matching your domain join method.
- Set NTFS permissions: On the file share, assign Storage File Data SMB Share Elevated Contributor to administrators and Storage File Data SMB Share Contributor to all AVD end users. Set NTFS-level permissions on the share root so users can create and access only their own profile directories.
- Configure FSLogix via Group Policy or Intune: On session hosts, configure the FSLogix registry keys — most importantly setting
VHDLocationsto the UNC path of your Azure Files share andEnabledto 1. FSLogix is pre-installed on Windows 10/11 Enterprise multi-session images; ensure you’re running the latest version for security and performance updates. - Use VHDX format: Configure FSLogix to use VHDX over VHD for profile containers, as VHDX supports larger sizes, offers better performance, and is more resilient to corruption.
- Enable Cloud Cache (optional): For multi-region deployments or disaster recovery scenarios, FSLogix Cloud Cache replicates profile data across multiple file share locations in real time, providing profile redundancy without manual backup and restore processes.
Step 6: Test & Validate Deployment
Before rolling out Azure Virtual Desktop to your full user base, conduct a structured validation to confirm every component of the deployment is functioning as expected. Catching issues at this stage is far less disruptive than troubleshooting problems in a live production environment.
- Test user connection: Using a test account with the Desktop Virtualization User role assigned, open the AVD web client or install the Windows App (available on Windows, macOS, iOS, Android, and web) and sign in. Verify that the workspace appears and the desktop launches successfully.
- Validate FSLogix profiles: Log in, make changes (create a desktop shortcut, change wallpaper, open and configure an application), log off, then log back in — if FSLogix is working correctly, all changes persist across sessions.
- Check session host health: In the Azure portal, navigate to Azure Virtual Desktop > Host pools > [your host pool] > Session hosts and verify all VMs show Available status with no health check failures.
- Review AVD Insights: Enable Azure Monitor for AVD (AVD Insights) via the Azure portal to get a real-time operational dashboard showing session counts, connection errors, host pool capacity, and gateway latency. This is invaluable for ongoing performance monitoring.
- Test application performance: Launch Microsoft 365 applications and any line-of-business apps, verify Teams meetings and audio/video work correctly with the WebRTC media optimization, and test OneDrive sync behavior under the user profile.
- Verify Multi-Session behavior: Simulate 2–3 concurrent users on a single session host and monitor CPU, memory, and disk I/O in Azure Monitor to validate that your chosen VM size can comfortably sustain the targeted session density.
Azure Virtual Desktop Security & Compliance
Security is not an afterthought in Azure Virtual Desktop — it is a core design principle. However, the built-in security capabilities of AVD still require deliberate configuration to achieve a hardened, compliance-ready deployment. Here is what you need to address:
- Conditional Access Policies: Use Microsoft Entra ID Conditional Access to enforce multi-factor authentication (MFA), device compliance requirements, and location-based access restrictions for AVD sessions. Require MFA for all users accessing AVD from non-compliant or unmanaged devices.
- Microsoft Defender for Endpoint: Onboard all session host VMs to Microsoft Defender for Endpoint for real-time endpoint protection, threat detection, and automated response. Use shared VM licensing for Defender on multi-session hosts to avoid per-device licensing costs.
- Just-in-Time (JIT) VM Access: Enable JIT VM access through Microsoft Defender for Cloud to eliminate persistent management ports (RDP/SSH) on session hosts and reduce attack surface from unauthorized access attempts.
- Azure Private Link: For maximum network security, configure Azure Private Link for AVD to route traffic between the AVD gateway and your session hosts over the Microsoft backbone network, eliminating exposure to the public internet entirely.
- Disk Encryption: Enable Azure Disk Encryption on all session host OS disks to protect data at rest. For regulated industries (healthcare, finance), consider customer-managed keys via Azure Key Vault for full cryptographic control.
- Session Recording and Auditing: Enable Azure Monitor diagnostic logs on your host pools and workspaces to capture connection events, user session activity, and configuration changes. Export logs to a Log Analytics workspace and create alerts for suspicious behavior such as unusual off-hours logins or excessive failed authentication attempts.
Apps4Rent’s managed AVD services include comprehensive security hardening aligned with HIPAA, SOC 2 Type II, and ISO 27001 frameworks — a significant advantage for regulated industries that need compliance documentation without building it from scratch.
Best Practices for Azure Virtual Desktop Deployment
The difference between an AVD deployment that delights users and one that generates constant support tickets often comes down to adherence to established best practices during planning and implementation. Here are the practices that experienced AVD architects consistently apply:
- Use the Azure Virtual Desktop Experience Estimator: Before provisioning VMs, use Microsoft’s AVD Experience Estimator to calculate the expected round-trip time (RTT) latency from your users’ locations to each Azure region. Choose the region that delivers sub-150ms RTT for your majority user base.
- Use Azure Compute Gallery for custom images: Rather than building session hosts from Azure Marketplace images and then manually installing applications post-deployment, create a custom golden image using Azure Compute Gallery (formerly Azure Shared Image Gallery). This ensures every new session host is identical, reduces provisioning time, and simplifies ongoing image management via versioned image definitions.
- Implement Autoscale for pooled host pools: Configure AVD’s built-in autoscale feature to automatically start additional session hosts during peak hours and shut them down (or deallocate them) during off-peak periods. This is one of the most impactful cost-control mechanisms available in AVD and can reduce compute costs by 40–60% for organizations with predictable usage patterns.
- Separate host pools by workload type: Create dedicated host pools for different user groups — a pooled host pool for office workers, a personal host pool for developers, and a GPU-enabled host pool for graphics users. Mixing workload types in a single host pool makes right-sizing impossible and leads to either over-provisioning or performance complaints.
- Keep session hosts stateless: Never allow users to store data directly on session host OS disks. Use FSLogix for profiles, OneDrive (with Known Folder Move) for documents and desktop files, and SharePoint/Teams for collaborative data. Stateless session hosts can be reimaged, redeployed, or replaced without any data loss — dramatically simplifying maintenance.
- Establish an image update cadence: Plan a regular schedule (monthly or quarterly) to update your golden image with the latest Windows updates, security patches, and application versions. Use Azure Compute Gallery versioning to maintain rollback capability if an updated image causes unexpected issues.
- Monitor proactively with AVD Insights: Configure Azure Monitor workbooks and alerts before go-live. Key metrics to alert on include session host availability, connection failure rates, user session latency (round-trip time), and FSLogix profile mount failure events.
Cost Optimization Tips for Azure Virtual Desktop
Azure Virtual Desktop can deliver dramatic cost savings compared to on-premises VDI — but only when the environment is actively optimized. Without careful cost management, it is easy to over-provision resources and negate the financial benefits of moving to the cloud.
- Leverage Azure Hybrid Benefit: If your organization has existing Windows Server licenses with Software Assurance, apply Azure Hybrid Benefit to your session host VMs to eliminate the Windows Server OS license cost, reducing VM costs by up to 40%.
- Use Azure Reserved Instances: For session hosts that run consistently (8+ hours per day), purchase Azure Reserved VM Instances (1-year or 3-year commitments) for savings of 40–72% compared to pay-as-you-go pricing. Combine reservations with autoscale by reserving capacity for your baseline load and using on-demand VMs only for peak overflows.
- Enable Autoscale aggressively: Configure autoscale to deallocate (not just stop) session hosts during off-hours. Deallocated VMs incur zero compute charges — you pay only for the OS disk storage, which is a fraction of compute cost. For a 100-user deployment, aggressive autoscaling can save $500–$2,000+ per month.
- Right-size your VMs: Conduct regular reviews of CPU, memory, and disk utilization metrics in Azure Monitor. If session hosts are consistently running below 50% utilization, downsize to a smaller VM SKU. If they are regularly exceeding 80%, upsize or add more session hosts to reduce per-user resource contention.
- Use Azure Spot Instances for non-production environments: For development, testing, or training environments where interruptions are acceptable, Azure Spot VMs offer savings of up to 90% compared to standard pricing. Never use Spot VMs for production session hosts, as they can be preempted by Azure with only 30 seconds of notice.
- Optimize storage costs: Use Azure Files Standard (LRS) tier for FSLogix profile storage in most deployments — it is significantly cheaper than Premium while offering adequate performance for typical knowledge worker profiles. Reserve Premium Files or Azure NetApp Files for high-performance workloads.
- Review Azure Cost Management dashboards weekly: Set up budget alerts in Azure Cost Management to notify you when AVD spending approaches or exceeds your monthly target. Tag all AVD resources consistently (e.g., Environment=Production, Workload=AVD) to enable granular cost attribution by department, project, or cost center.
| Cost Optimization Method | Estimated Savings | Best Applied To | Complexity |
| Azure Hybrid Benefit | Up to 40% on compute | Orgs with existing Windows SA licenses | Low — toggle in portal |
| Reserved VM Instances (1-year) | 40–60% vs pay-as-you-go | Baseline session hosts running 8+ hrs/day | Low — purchase in portal |
| Reserved VM Instances (3-year) | Up to 72% vs pay-as-you-go | Long-term production workloads | Low — commitment required |
| Autoscale (Deallocate off-hours) | 40–60% monthly compute | Pooled host pools with predictable hours | Medium — policy configuration |
| Azure Spot VMs | Up to 90% vs standard | Dev / test / training environments only | Low — select at VM creation |
| VM Right-Sizing | Varies — 20–50% typical | Over-provisioned session hosts | Medium — ongoing monitoring |
| Azure Files Standard LRS (FSLogix) | 60–80% vs Premium tier | Standard knowledge worker profiles | Low — tier selection |
Azure Virtual Desktop vs Windows 365
A common question when evaluating cloud desktops in 2026 is: should we use Azure Virtual Desktop or Windows 365? Both are Microsoft cloud desktop platforms, but they serve different organizational needs and technical profiles.
- Azure Virtual Desktop is the right choice for organizations that need maximum flexibility, control, and cost efficiency. AVD supports multi-session VMs, custom images, autoscaling, GPU workloads, custom networking, and deep integration with on-premises infrastructure. It requires meaningful IT expertise to deploy and manage, and costs scale with actual usage — making it highly economical for organizations that can manage workloads efficiently.
- Windows 365 is the right choice for organizations that prioritize simplicity over flexibility. Windows 365 Cloud PCs are provisioned in minutes from the Microsoft Intune admin center with no Azure knowledge required, and billing is a fixed per-user, per-month fee regardless of usage — eliminating the variable cost unpredictability of AVD. However, Windows 365 does not support multi-session, custom networking, or GPU-enabled Cloud PCs in most plans, and costs are typically higher per user than an optimized AVD deployment.
| Feature | Azure Virtual Desktop (AVD) | Windows 365 Cloud PC |
| Deployment Complexity | Moderate — requires Azure expertise | Low — Intune-managed, no Azure needed |
| Multi-Session VMs | Yes — multiple users per VM | No — one user per Cloud PC |
| Pricing Model | Variable — pay for what you use | Fixed — flat per-user per-month |
| Cost at Scale | Lower with autoscale and reservations | Predictable but higher per-user |
| Custom Images | Yes — full image control via Azure Gallery | Limited — basic image customization |
| Autoscaling | Yes — built-in autoscale policies | No — static provisioning |
| GPU Support | Yes — NV-series GPU VMs | No GPU Cloud PC plans |
| Custom Networking | Yes — VNet, NSG, Private Link | Limited — Microsoft-hosted network |
| FSLogix Profile Management | Yes — required for pooled pools | Not needed — persistent Cloud PC |
| Admin Tool | Azure Portal / CLI / PowerShell | Microsoft Intune admin center |
| Best For | IT-mature orgs wanting cost control | Orgs wanting simplicity over savings |
For a detailed side-by-side comparison of features, pricing, and use cases, read our guide: Windows 365 Cloud PC vs Azure Virtual Desktop. Apps4Rent offers fully managed services for both platforms — our team can help you evaluate which solution best fits your organization’s requirements and budget.
Common Azure Virtual Desktop Setup Issues & Fixes
Even well-planned AVD deployments encounter issues. Here are the most common problems encountered during and after Azure Virtual Desktop setup, along with their root causes and resolutions:
- Session hosts showing “Unavailable” in the portal: This typically indicates the AVD agent is not running, cannot reach the AVD service endpoints, or the VM failed to join the domain. Verify outbound network connectivity from the VNet to AVD service URLs, confirm the domain join completed successfully, and check the AVD agent installation logs at
C:\Windows\Temp\ScriptLog.log. - Users cannot see the workspace in the AVD client: Most commonly caused by users not being assigned the Desktop Virtualization User role on the application group, or the application group not being registered to the workspace. Verify both the role assignment in IAM and the workspace registration under the application group’s Properties blade.
- FSLogix profile fails to load — users get temporary profiles: This almost always indicates a permissions issue with the Azure Files share. Verify that the storage account has AD authentication enabled, the user’s account has the Storage File Data SMB Share Contributor RBAC role, and the NTFS permissions on the share root allow the user to create subfolders. Check FSLogix event logs on the session host under
Applications and Services Logs > Microsoft > FSLogix > Profile > Operational. - Poor performance or slow application launch times: Most performance issues trace back to VM undersizing, storage latency, or suboptimal image configuration. Use AVD Insights to identify which session hosts show elevated CPU or memory, review FSLogix profile size (large profiles slow mount times), and verify session hosts are using Premium SSD OS disks rather than Standard HDD or Standard SSD.
- Microsoft Teams audio/video not working correctly: Teams in AVD requires WebRTC media optimization to redirect audio and video processing to the local endpoint device. This requires the Teams WebRTC optimization pack to be installed on session hosts and the AVD client version on user devices to support media redirection. Verify both components are at current versions and that the user’s local device has functioning audio/video hardware.
- Users being disconnected unexpectedly: Unexpected disconnections often result from aggressive idle session timeouts configured in host pool RDP properties, session host VM memory exhaustion causing Windows to terminate sessions, or transient network issues between the user and the AVD gateway. Review session host resource utilization during the disconnection timeframe in Azure Monitor and adjust timeout settings appropriately for your user population.
The table below summarizes the most common AVD issues along with their root cause and fastest resolution path:
| Issue | Root Cause | Resolution |
| Session host shows “Unavailable” | AVD agent not running, failed domain join, or blocked outbound connectivity | Check ScriptLog.log, verify VNet DNS, confirm domain join status |
| Workspace not visible in AVD client | Desktop Virtualization User role not assigned, or app group not registered to workspace | Verify IAM role assignment and workspace registration in portal |
| FSLogix loads temporary profile | Missing RBAC on Azure Files share or incorrect NTFS permissions | Assign SMB Contributor role, verify NTFS, check FSLogix Operational event log |
| Slow logon or application launch | VM undersizing, large FSLogix profile, or HDD OS disk | Upsize VM, clean up profile bloat, switch to Premium SSD OS disk |
| Teams audio/video not working | WebRTC media optimization not installed or outdated AVD client | Install Teams WebRTC pack on session hosts, update Windows App client |
| Unexpected session disconnections | Idle timeout too aggressive, VM memory exhaustion, or network flap | Adjust RDP timeout settings, right-size VMs, review Azure Monitor during incident window |
| Black screen on session launch | Graphics driver issue or GPU driver mismatch on session host | Reinstall NVIDIA GRID driver matching the VM generation, restart session host |
Frequently Asked Questions About Azure Virtual Desktop Setup
-
How long does Azure Virtual Desktop setup take?
A basic proof-of-concept AVD environment with 1 host pool, 2 session hosts, and 5 test users can be deployed in 2–4 hours by an experienced Azure administrator. A production deployment with custom golden images, FSLogix, autoscale, monitoring, and security hardening typically requires 3–10 business days depending on environment complexity and organizational change management requirements. Apps4Rent’s managed AVD onboarding typically completes within 3–5 business days.
-
What is the minimum number of users required for Azure Virtual Desktop to make financial sense?
AVD’s multi-session capability makes it cost-effective at relatively small scale — even deployments of 10–20 users can see meaningful savings over traditional VDI or providing physical PCs. The financial case strengthens significantly as user counts grow, particularly for organizations with predictable usage patterns that benefit from aggressive autoscaling.
-
Can AVD session hosts run applications that require local administrator rights?
Yes, but with caution. Granting users local administrator rights on shared, multi-session VMs creates significant security risks and is strongly discouraged. Instead, use solutions like Microsoft Intune elevation policies or third-party privilege management tools to grant time-limited, audited elevation for specific applications or tasks without giving persistent admin rights.
-
Does Azure Virtual Desktop support GPU workloads like CAD or video rendering?
Yes. AVD supports GPU-enabled session hosts using Azure’s NV-series (NVIDIA GPU-accelerated) or NVads A10 v5-series VMs. GPU session hosts require the appropriate NVIDIA GRID driver to be installed and configured on the image. For GPU workloads, personal (dedicated) host pools are typically preferred over pooled host pools to ensure consistent GPU resource allocation per user.
-
How does Azure Virtual Desktop handle data residency and sovereignty requirements?
AVD session hosts are deployed in the Azure region you select, ensuring user session data and profile data remain within that geography. The AVD control plane (broker, gateway, diagnostics) operates from Microsoft-managed global infrastructure, though user data processed within sessions stays within the session host VM’s region. For strict data sovereignty requirements, consult your compliance team and refer to Microsoft’s AVD data locations documentation.
-
What is the difference between pooled and personal host pools in AVD?
Pooled host pools allow multiple users to share session host VMs simultaneously, maximizing efficiency through multi-session Windows. Personal host pools assign each user a dedicated VM that only they log into — similar to a traditional virtual PC. Pooled pools are best for most knowledge workers; personal pools suit developers, power users, or scenarios requiring persistent local application installations.
-
Can I use my existing Active Directory with Azure Virtual Desktop?
Yes. AVD supports traditional Active Directory Domain Services (AD DS) domain joins, provided your domain controllers are accessible from the AVD virtual network (via Azure VPN Gateway or ExpressRoute for on-premises DCs, or as Azure-hosted VMs). Your AD DS must sync to Microsoft Entra ID using Microsoft Entra Connect. Modern cloud-native deployments use Entra ID Join instead, eliminating the dependency on AD DS entirely.
Conclusion: Is Azure Virtual Desktop Right for Your Organization?
Azure Virtual Desktop is the most capable, cost-effective, and Microsoft-integrated cloud desktop platform available in 2026. When properly deployed — with the right host pool architecture, FSLogix profile management, security hardening, and cost optimization in place — AVD delivers a desktop experience that is indistinguishable from a local PC while enabling IT to manage, secure, and scale the entire environment from a central cloud console.
The setup process, as this guide demonstrates, is thorough. Between Active Directory configuration, host pool creation, session host deployment, FSLogix setup, security policy enforcement, and ongoing monitoring, a production-ready AVD environment involves dozens of interdependent decisions. Each one done wrong adds friction for users and complexity for IT.
That is exactly why many organizations — from 10-user SMBs to enterprise teams of thousands — choose to partner with Apps4Rent for their Azure Virtual Desktop deployment and management. With over 20 years of Microsoft cloud experience, Microsoft Solutions Partner across five key areas: Modern Work, Security, Data & AI (Azure), Digital & App Innovation (Azure), and Infrastructure (Azure), and more than 10,000 successful cloud migrations, Apps4Rent handles the full AVD lifecycle: architecture, deployment, security hardening, ongoing management, user support, and cost optimization. You get a high-performance, enterprise-grade cloud desktop without needing an in-house Azure expert on staff.
Ready to Set Up Azure Virtual Desktop — Without the Complexity?
Talk to an Apps4Rent AVD specialist today. We’ll assess your environment, recommend the right architecture, and have your cloud desktop live in days — not weeks.
Plans start from $66/month with 24/7 live support, daily backups, and SSD storage included. No hidden fees. No long-term lock-in.





